The web application was vulnerable to SQL Injection, one of the most dangerous vulnerabilities for an application. A vulnerability scanning tool would have detected it and given information on how to fix it. There was no WAF ( Web Application Firewall) in place to detect the SQL Injection exploitation.
What is SQL injection?
SQL Injection is a sort of infusion assault that makes it conceivable to execute malicious SQL statements. These statements control a database server behind a web application.
What is assertassailants SQL injection and how to prevent it?
Assailants can utilize SQL Injection vulnerabilities to sidestep application safety efforts. They can circumvent authentication and authorization of a page or web application and recover the content of the whole SQL database.
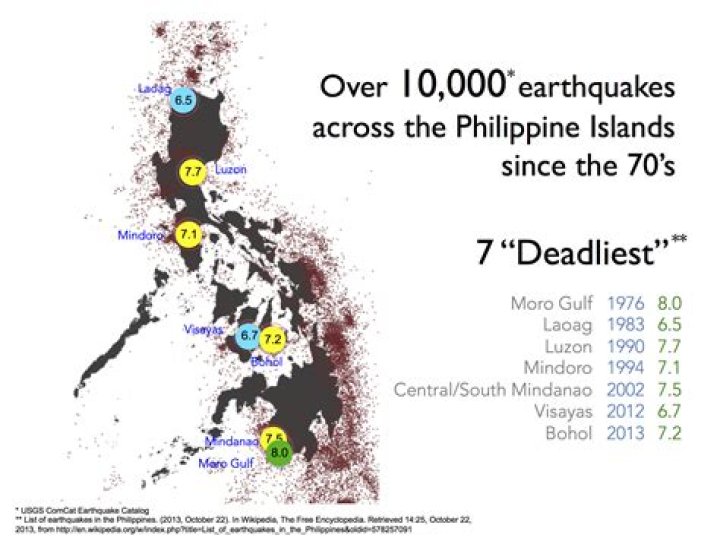
How do I find out what version of metasploitable 2 is running?
The first step towards doing what we want to achieve is a service scan that looks at all the 65535 ports of Metasploitable 2 to see what’s running where and with what version. You will notice the result in the image below.
How do you protect against SQL injection?
If you use stored procedures, you should use parameters as their input. If you cannot use stored procedures, you can still use parameters, as shown in the following code example. Filtering input may also be helpful in protecting against SQL injection by removing escape characters.
What are the possible attack vectors for SQL injection?
Other possible attack vectors include HTTP cookie data and the HTTP User-Agent and Referer header values. Some SQL injection vulnerabilities may only be exploitable via authenticated unprivileged user accounts, depending upon where the application fails to sanitize the input.
What are some common examples of SQL injection?
Some common SQL injection examples include: Retrieving hidden data, where you can modify an SQL query to return additional results. Subverting application logic, where you can change a query to interfere with the application’s logic. UNION attacks, where you can retrieve data from different database tables.